A Network of Sensors for Threat Detection
05/12/2023

By Graciela Martínez Head of LACNIC CSIRT and Guillermo Pereyra Security Analyst at LACNIC CSIRT
LACNIC’s Computer Security Incident Response Team (LACNIC CSIRT) has deployed a sensor network in the region for the purpose of learning about potential cyberattacks and threats in Latin America and the Caribbean in real time.
This network is known as a honey net, and the data it provides allows us to take a proactive approach and issue warnings about threats that our members’ networks may suffer in real time. This means they can take actions to prevent potential attacks.
The honey net network comprises a series of interactive devices connected to the Internet in various countries across the region that allow viewing security events in real time and understanding the modus operandi of the most common attacks. This data makes it possible to generate knowledge and analyze how attackers behave.
A honeypot is a device connected to the Internet that passively records the traffic it receives. Any interaction with a sensor is potentially malicious, as the sensor does not provide any actual services. The sensor’s operation is quite simple: it simulates an actual server with very basic security configurations designed specifically to be targeted by hackers.
This makes a honeypot a powerful tool to detect malicious activities. LACNIC CSIRT has deployed a distributed set of honeypots, known as a honey net. In particular, the LACNIC HoneyNet focuses on logging access attempts to ssh (secure shell) accounts exposed to the internet. The user/key pairs that attackers attempt to use and the IP addresses originating these attempts are of particular interest.
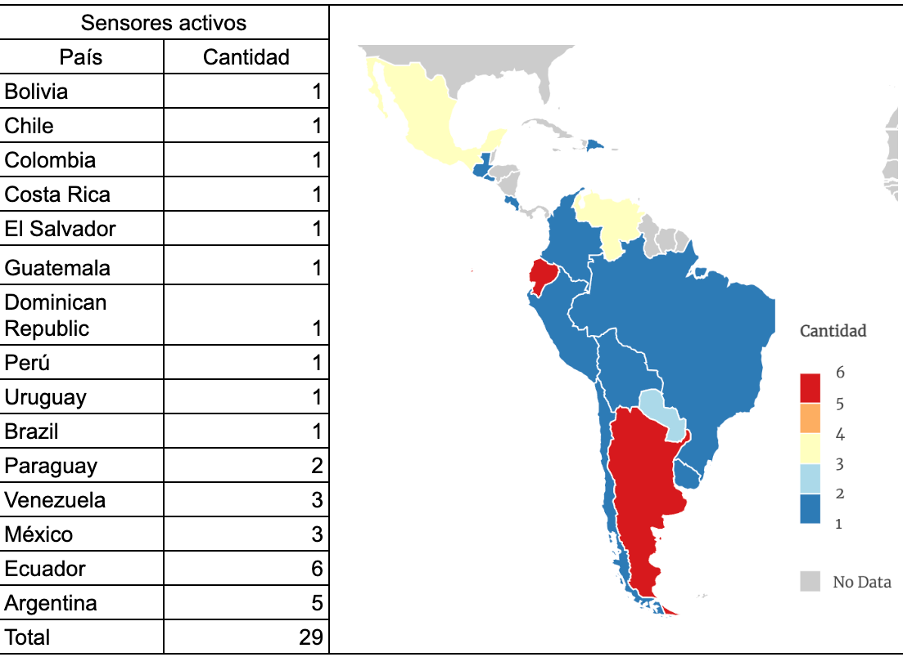
This year CSIRT’s honey net network incorporated seven new sensors: one in Chile, two in Ecuador, one in Peru, and three in Venezuela, thus totaling 29 sensors, six of them operating in dual-stack mode (IPv4-IPv6).
We invite you to join the LACNIC HoneyNet initiative by installing a sensor in your organization’s network. This will allow you to implement proactive actions in the systems protecting your networks.
If you are interested in participating, please email csirt@lacnic.net.